Table of Contents
ToggleOne Agent. 5 Systems. Zero Human Clicks. Ready for Enterprises?
An AI agent schedules meetings, pulls internal reports, updates a CRM, triggers a workflow, and sends a summary, without human intervention.
OpenClaw represents a class of autonomous agents that don’t stop at responses. They access systems, execute actions, and operate using real enterprise identities and permissions. This type of advanced AI product is pushing the boundaries of what’s possible in enterprise automation.
This is where enterprise questions surface.
If one agent touches five systems:
- Does it carry one identity or many?
- Who approves its access?
- How is activity logged and reviewed?
- What defines acceptable behavior when the agent decides the next step?
These questions sit at the center of enterprise identity, access control, and auditability, areas designed for employees, not autonomous software entities that operate continuously.
OpenClaw has made this gap visible.
What began in developer environments is now forcing enterprises to re-examine how identity, control, and accountability work when actions are no longer human-initiated.
This blog looks at what OpenClaw signals for enterprises, and why autonomous agents are pushing identity and security models into unfamiliar territory.
So What Is OpenClaw Really? One Agent, 3 Capabilities Enterprises Can’t Ignore
OpenClaw is an open-source autonomous agent framework designed to plan tasks, take actions, and work across systems, not just generate text.
From an enterprise lens, OpenClaw stands out for three core capabilities.
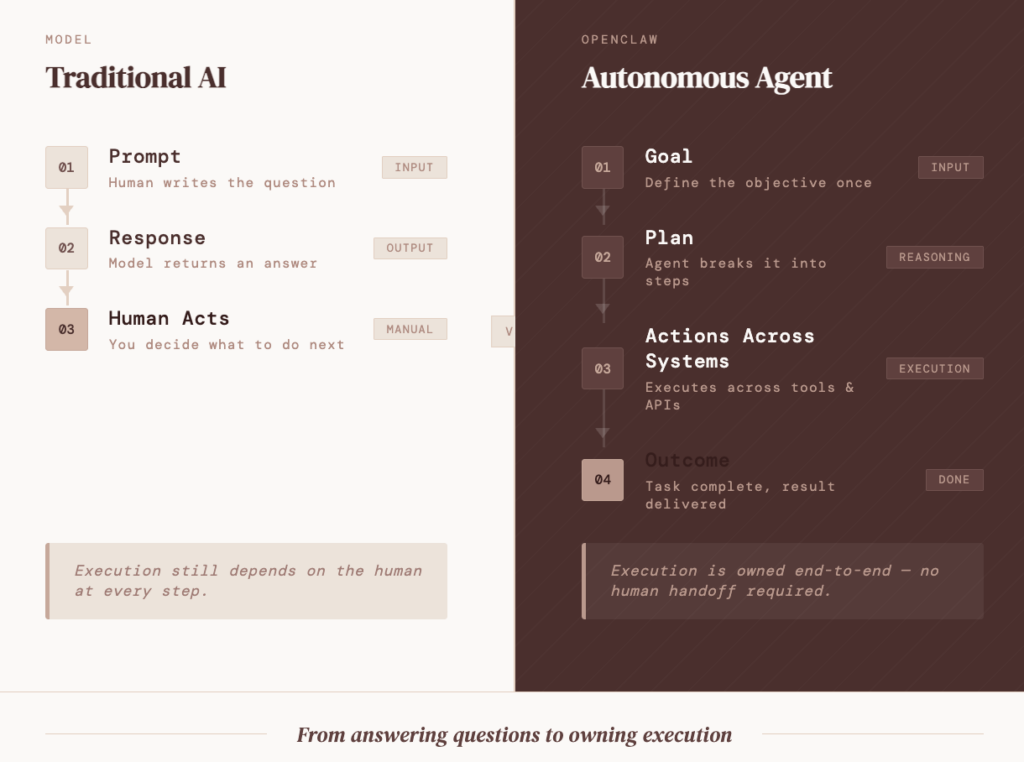
1. It plans work, not prompts
OpenClaw doesn’t stop at a single instruction. It breaks an objective into steps and decides the sequence.
Example
“Prepare a weekly sales update” turns into:
- Pulling data from internal systems
- Structuring the information
- Validating outputs
- Sharing results with stakeholders
This is task ownership, not prompt completion.
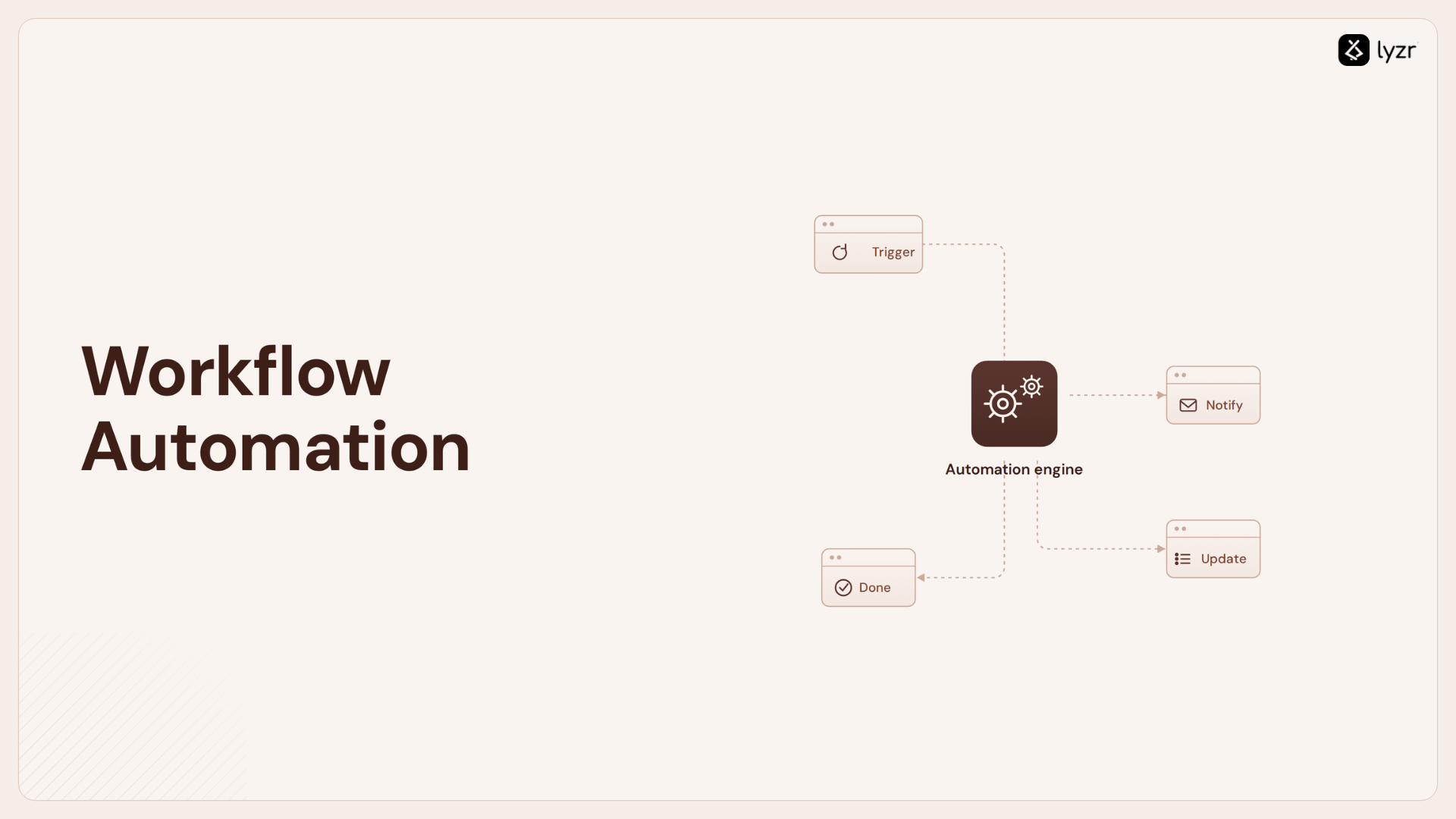
2. It takes real actions
The agent can execute actions such as:
- Reading and sending emails
- Calling internal or external APIs
- Running scripts
- Updating systems like CRMs or ticketing tools
All of this happens using the credentials and permissions available in its environment.
For enterprises, this is the shift that matters most, actions now happen without a human clicking through systems.
3. It works across systems, not inside one
OpenClaw isn’t tied to a single interface. It can operate across collaboration tools, internal applications, and services, effectively sitting between systems.
That cross-system behavior is what makes it useful for automation, and risky without controls.
Where Enterprises See Value, and Why Interest Builds Faster Than Expected??
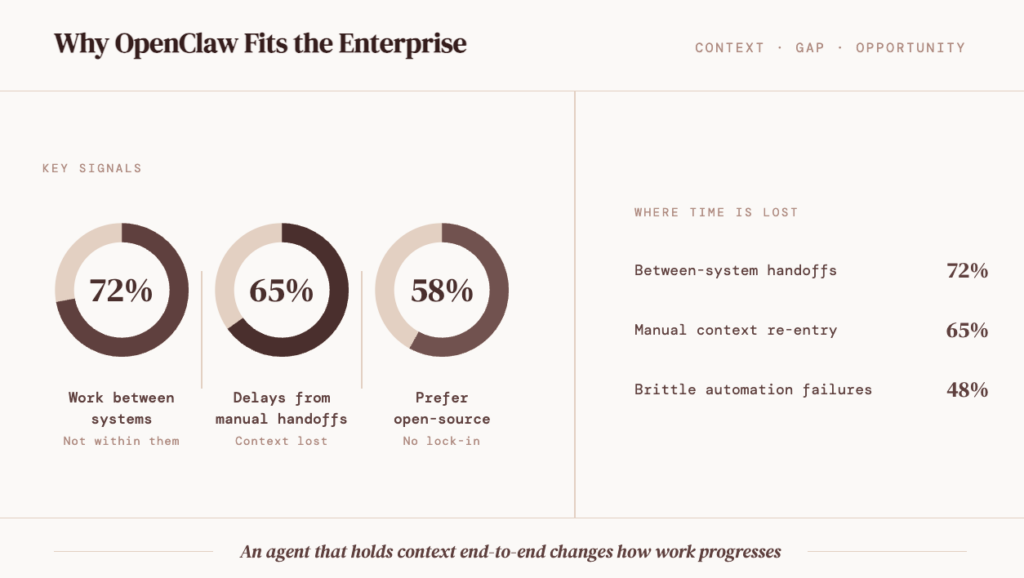
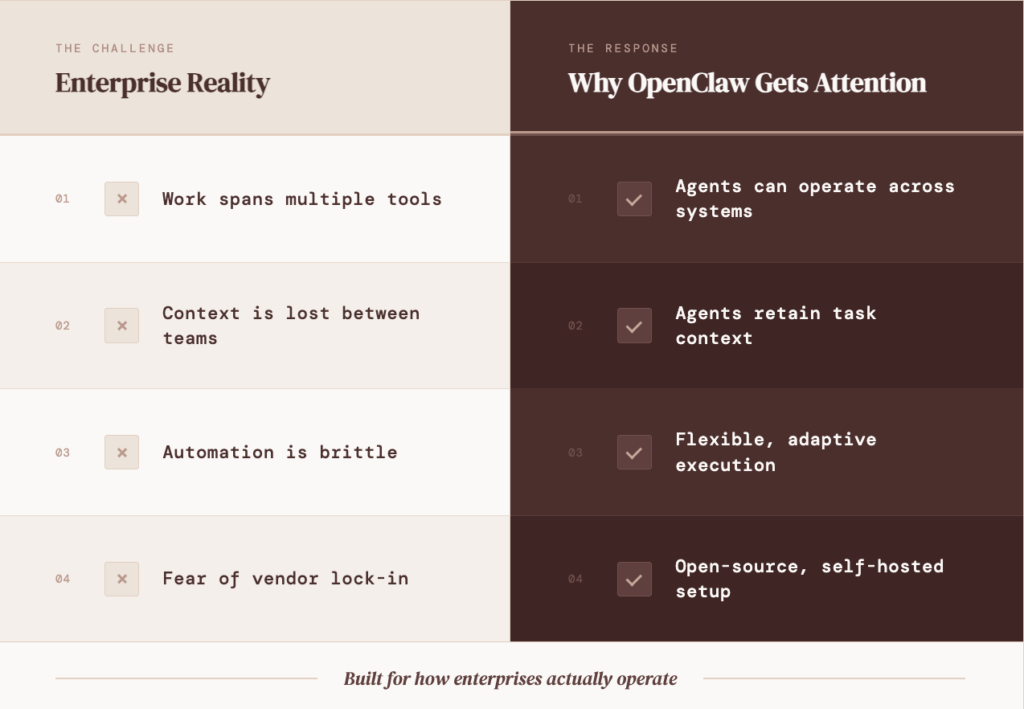
OpenClaw enters enterprise conversations because it fits work teams already do. The interest grows when it maps to gaps that are currently handled through manual coordination.
Much of enterprise work happens between systems, not within them. Data moves across tools, waits for review, and slows at handoffs.
An agent that operates across these boundaries and holds context end-to-end changes how that work progresses.
Enterprises stay cautious. Automation often brings lock-in or limited scope, which is why OpenClaw’s open-source, self-hosted setup appeals for controlled internal experimentation.
Where the value shows up most often
- Cross-system operational work: Tasks that require pulling, validating, and pushing data across multiple tools
- Processes with frequent handoffs: Work that slows down due to coordination rather than decision-making
- Internal automation experiments: Use cases that teams want to test without committing to long-term platforms
Why this resonates inside enterprises
The trade-off enterprises notice quickly
The same traits that create value also raise concerns:
- Cross-system reach increases blast radius
- Persistent context complicates audits
- Independent execution challenges accountability
That’s why OpenClaw rarely stays a productivity discussion for long.
A Wake-Up Call for Enterprises: When Autonomy Outruns Security
OpenClaw offers clear benefits, local-first execution, flexibility, and autonomy. But its rapid adoption has also exposed a hard truth: security assumptions built for humans don’t hold when agents act independently with delegated authority.
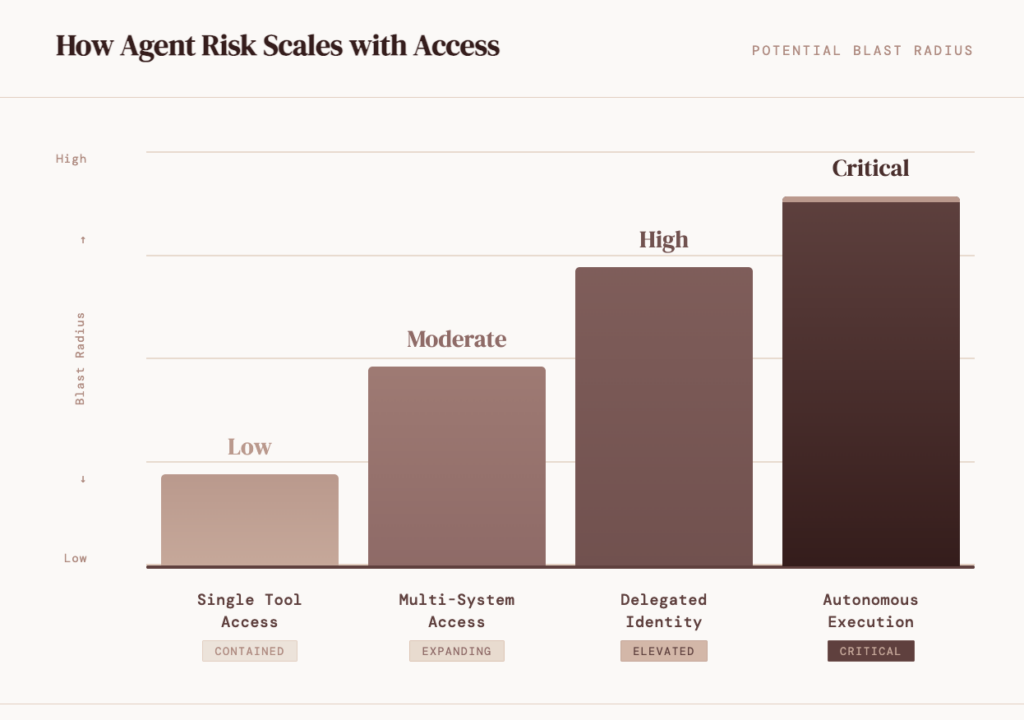
Multiple security investigations have surfaced gaps across the ecosystem, spanning vulnerabilities, identity sprawl, and untrusted extensions.
What security teams have already found??
- Mav Levin at DepthFirst disclosed a 1-click remote code execution flaw (CVE-2026-25253), where a malicious link could leak tokens and run arbitrary shell commands.
- Researchers at Wiz, led by Gal Nagli, uncovered a misconfigured Moltbook database exposing 1.5 million API keys and 35,000 emails, with just 17,000 identities controlling 1.5 million bots.
- Koi Security identified 341 malicious skills in the ClawHub marketplace, including coordinated infostealer campaigns.
- Permiso demonstrated prompt-injection attacks that poisoned agent memory and triggered unauthorized actions, including attempted crypto transactions.
The underlying gap
| Enterprise assumption | Autonomous agent reality |
| Users initiate actions | Agents act independently |
| Permissions are scoped | Access is often inherited |
| Logs explain behavior | Intent is hard to reconstruct |
The takeaway
OpenClaw highlights both the promise and the risk of autonomous agents. The lesson isn’t to avoid them, it’s to recognize that agent security is identity security, and small weaknesses can scale fast.
Next, we’ll look at three identity security pressure points enterprises must address before autonomous agents move beyond experimentation.
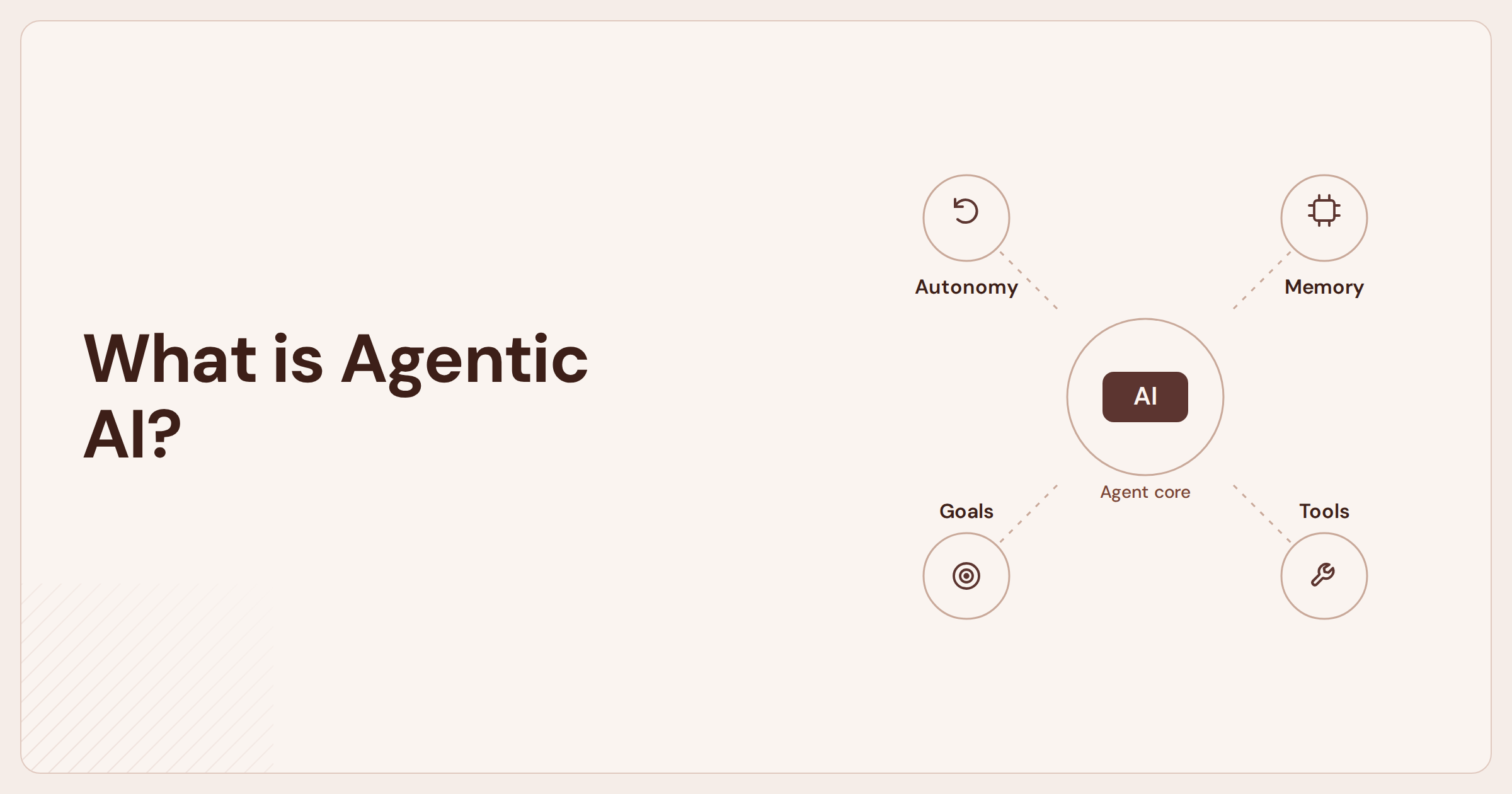
What This Means for Enterprises, and Why Platforms Like Lyzr Exist
The issues exposed by OpenClaw are not a reason enterprises are stepping back from autonomous agents.
They’re the reason enterprises are becoming more deliberate about how agents are built, deployed, and governed.
Most organizations don’t want agents that simply run locally and “figure things out.”
They want agents that operate within clear boundaries, with visibility into what they can access, how they behave, and why actions were taken.
This is where the conversation starts shifting away from raw frameworks and toward enterprise-grade agent platforms.
The enterprise expectation has changed
After seeing how quickly risks surface, enterprises start asking different questions:
- How is agent access scoped across systems?
- Can behavior be constrained without rewriting logic?
- Is there a way to review why an agent acted, not just what it did?
- Can experimentation happen without exposing production identities?
These aren’t questions OpenClaw was designed to answer on its own, and that’s not a flaw. It’s a reflection of its origins as a developer-first framework.
Where Lyzr fits into this shift
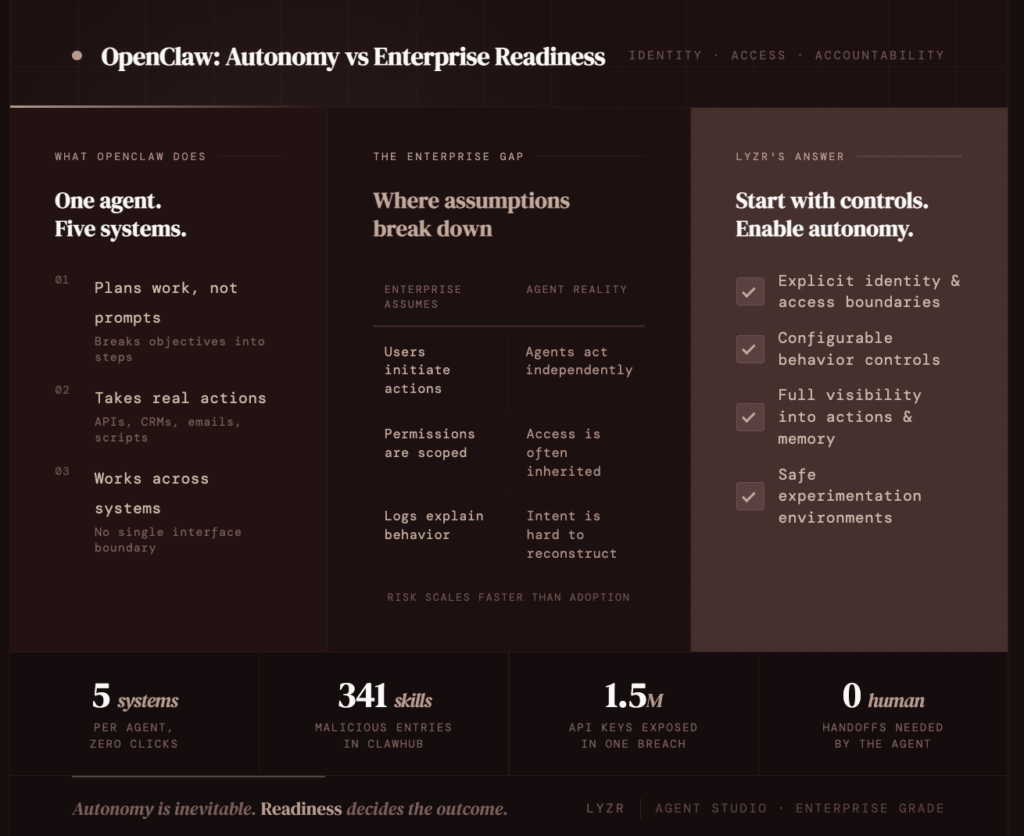
Lyzr approaches agents from the opposite direction:
start with enterprise controls, then enable autonomy.
Instead of assuming trust and adding guardrails later, Lyzr is designed around:
- Explicit identity and access boundaries
- Configurable controls for agent behavior
- Visibility into actions, memory, and decision paths
- Safe environments for experimentation before production rollout
This allows enterprises to explore autonomous agents without inheriting the full blast radius seen in open, ungoverned ecosystems.
The bigger takeaway
OpenClaw highlights what’s possible when agents are unconstrained. Lyzr addresses what’s required when agents operate in enterprise environments.
The future isn’t choosing between autonomy and control. It’s building agents where autonomy exists inside clearly defined limits.
Conclusion: Autonomy Is Here. Readiness Decides the Outcome.
OpenClaw has made autonomous agents real for enterprises, systems that don’t just respond, but act across environments.
The value is clear. So are the risks. Recent security findings show what happens when agents operate with broad authority and limited controls.
This isn’t a flaw unique to OpenClaw; it’s a signal that enterprise identity and governance models weren’t designed for autonomous actors.
Enterprises don’t need to slow adoption. They need clearer boundaries around access, behavior, and accountability before agents move into production.
That’s why the focus is shifting from experimentation to readiness, and toward platforms like Lyzr Agent Studio, where autonomy operates within defined controls.
Autonomous agents are inevitable. The advantage will belong to organizations that adopt them deliberately, not blindly.
Book A Demo: Click Here
Join our Slack: Click Here
Link to our GitHub: Click Here